The common approach to meeting the challenges of managing data is to map the process of creating and using data to a lifecycle. This is sometimes referred to as data lifecycle management (DLM) or information lifecycle management (ILM).
The purpose of such an approach is to allow an organization to identify the distinct phases data goes through, and then within each step or phase, to identify different security controls that should be in place.
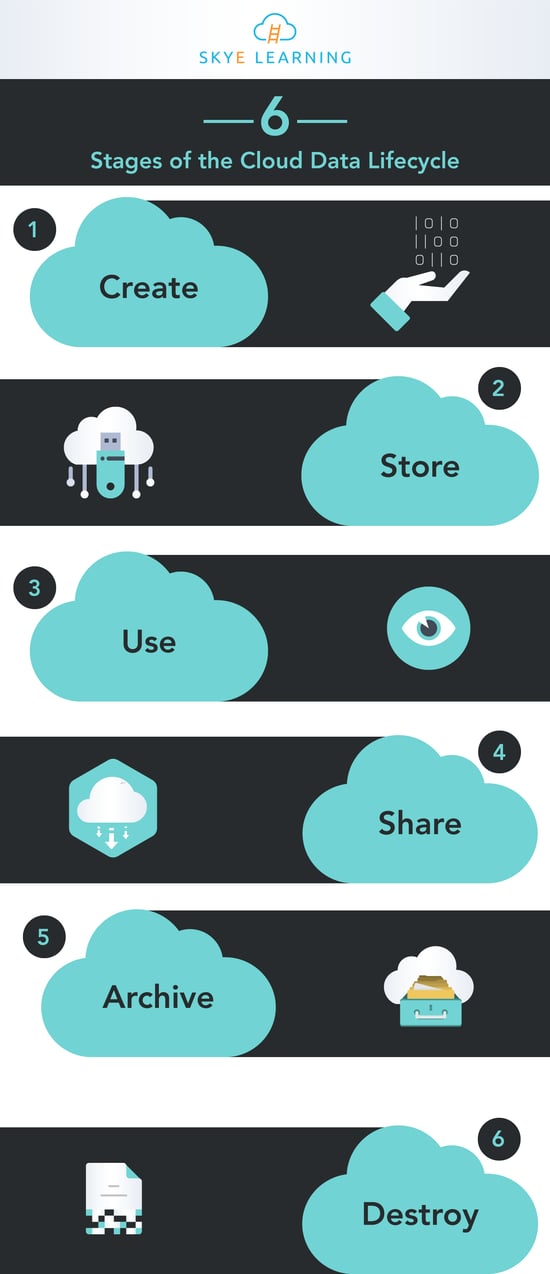
While there are differing models of the data lifecycle, the Cloud Security Alliance (CSA) has developed the cloud data lifecycle, recognizing six distinct steps that data in the cloud goes through. A particular phase or step can be skipped, or data may switch back and forth between different phases. Check out our latest infographic to learn more.
Skye Learning Cybersecurity & CISSP® Courses






